CSF/LFD security notifications
- Category : WHM questions
- Posted on : Sep 11, 2021
- Views : 1,897
- By : HostSEO

ConfigServer Security & Firewall (CSF) is a Stateful Packet Inspection (SPI) firewall, login/intrusion detection, and security application for Linux servers provided by ConfigServer.
Login Failure Daemon (LFD) is a daemon process that runs on our servers, which uses CSF for server security.
CSF and LFD come pre-installed on our servers with cPanel and offer many helpful features to ensure server security.
In case it’s not already installed, you can find information on how to install CSF/LFD as well as how to work with the CSF plugin.
One of the many benefits of CSF and LFD is that they provide you with various notifications to help keep track of important events taking place in your server. Please note that these notifications only appear if you have a VPS or Dedicated Server.
1. Excessive resource usage alert
2. System integrity alert
3. Suspicious process alert
4. Alert about IP block
5. Email queue size alert
6. Email script alert
7. Excessive processes alert
1. Excessive resource usage alert
- Notifications about memory exceeded
- Notifications about time exceeded
- How to disable notifications
Let’s start with a type of notification you’ll most likely often face. LFD has a feature in place to watch running processes to see if they are using too many resources. For some of these resources, you can even configure how much counts as too much. In some cases, if a process is using more resources than expected, this can indicate a security issue. Even if it does not, it should be investigated to check whether or not something is misconfigured, which can cause loading issues on the server.
By default, these notifications look like this:
From: root
To: root
Subject: lfd on [hostname]: Excessive resource usage: [user] ([pid])
Time: [time]
Account: [user]
Resource: [resource]
Exceeded: [level]
Executable: [exe]
Command Line: [cmd]
PID: [pid]
Killed: [kill]
- root in the From: and To: lines are usually replaced by root@
- [hostname] is replaced by the server's hostname
- [user] is replaced by the user the process in question is running under
With this particular feature, you will most likely encounter false-positives. The purpose of the feature is to bring to your attention the processes that have been running for a long time under a user account, which ones that are consuming a lot of memory or the ports that remain open outside of your server.
Here is an example LFD email alert when memory is exceeded:
Time: Mon Nov 14 09:41:10 2016 +0530
Account: xxxxxx
Resource: Virtual Memory Size
Exceeded: 205 > 200 (MB)
Executable: /usr/bin/php
Command Line: /usr/bin/php /home/xxxxxx/public_html/index.php
PID: 26953 (Parent PID:24974)
Killed: No
This alert is sent by LFD when a process uses more memory resources than defined in the CSF configuration file.
Here is an example LFD email alert when time is exceeded:
Time: Mon Nov 14 09:41:10 2016 +0530
Account: xxxxxx
Resource: Virtual Memory Size
Exceeded: 125389 > 1800 (seconds)
Executable: /usr/bin/php
Command Line: /usr/bin/php /home/xxxxxx/public_html/index.php
PID: 28429 (Parent PID:26561)
Killed: No
This alert is sent by LFD when a process takes more time to execute than as defined in the CSF configuration file.
Sometimes you may find yourself receiving a lot of resource usage alert emails and might want to get them disabled. Make sure to double check that they are indeed false-positives before ignoring or disabling them.
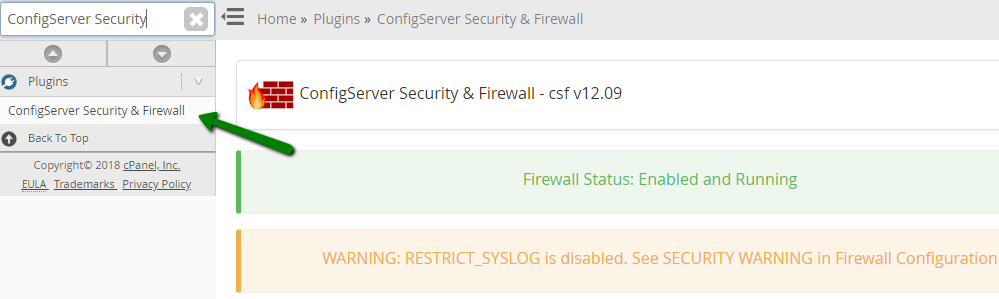
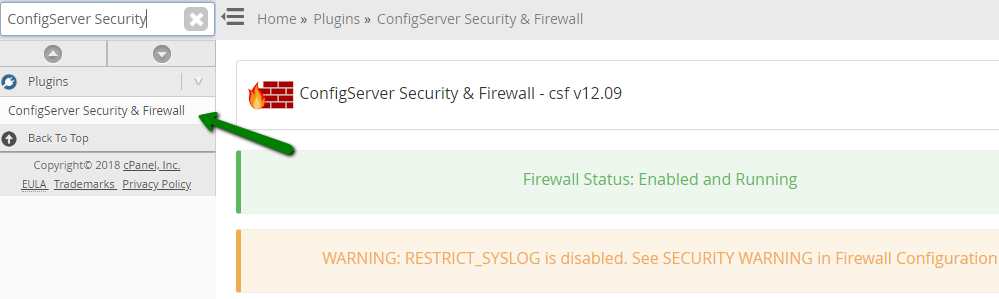
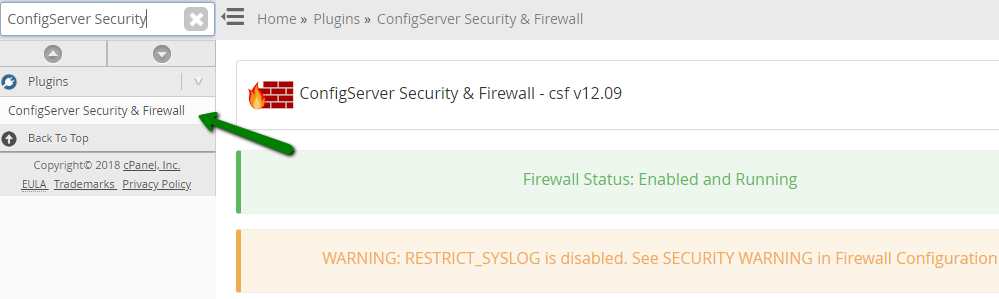
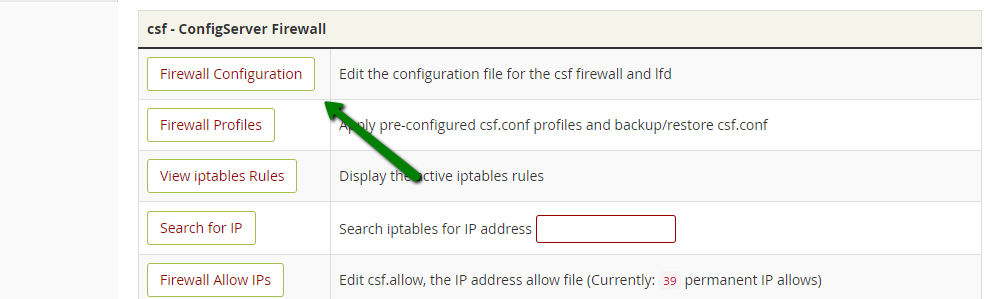
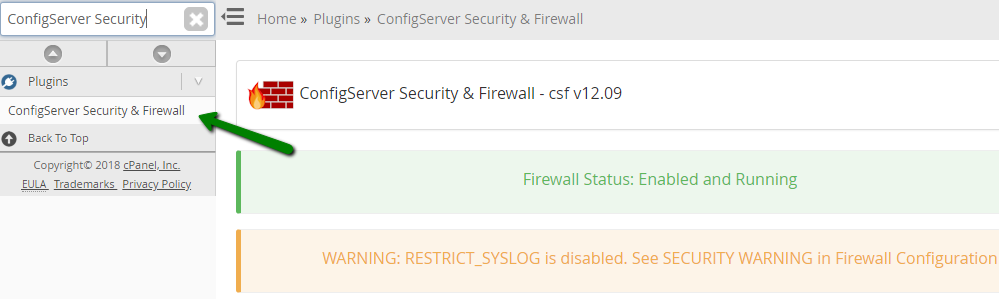
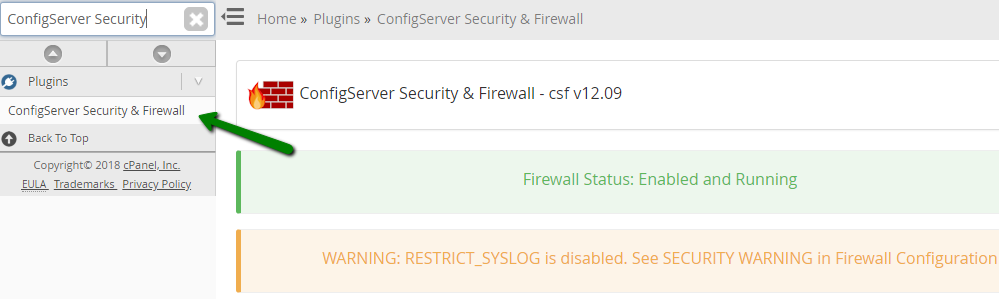
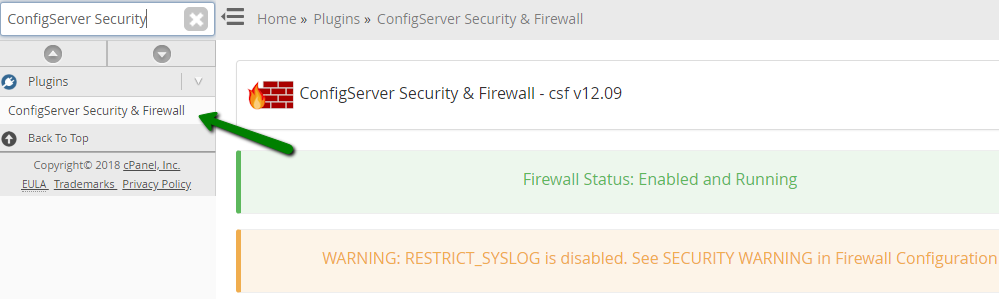
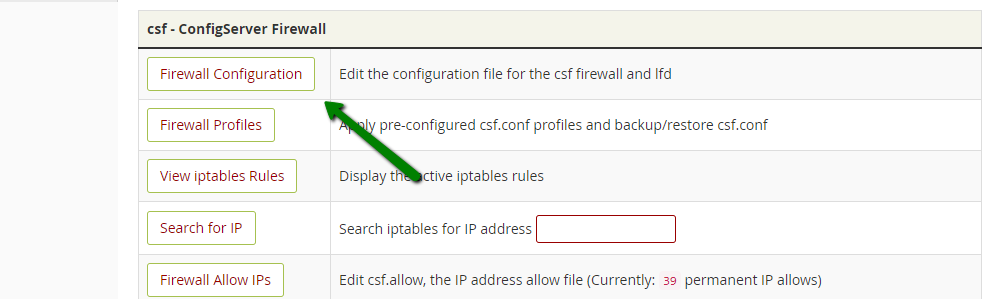
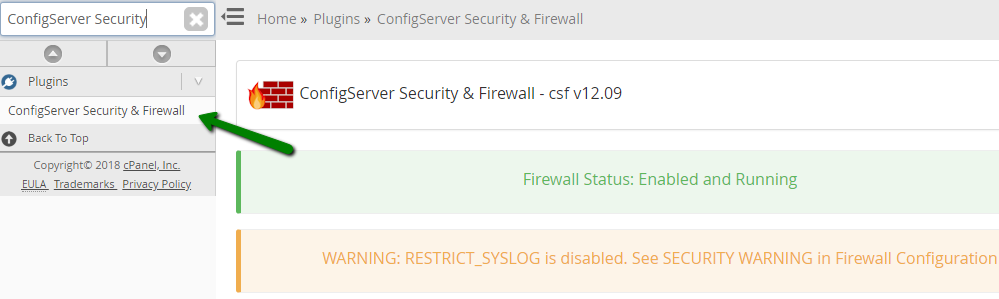
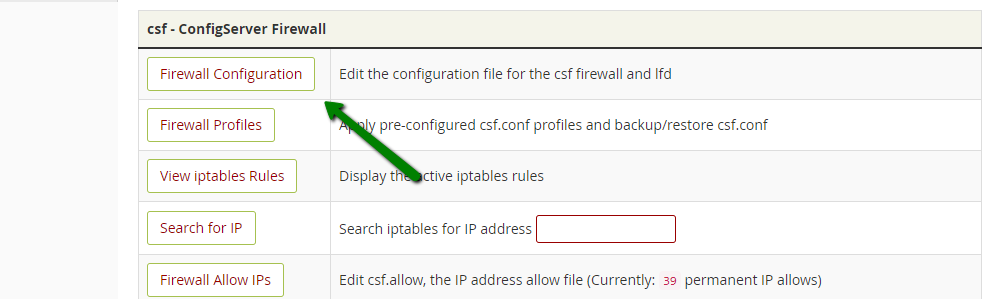
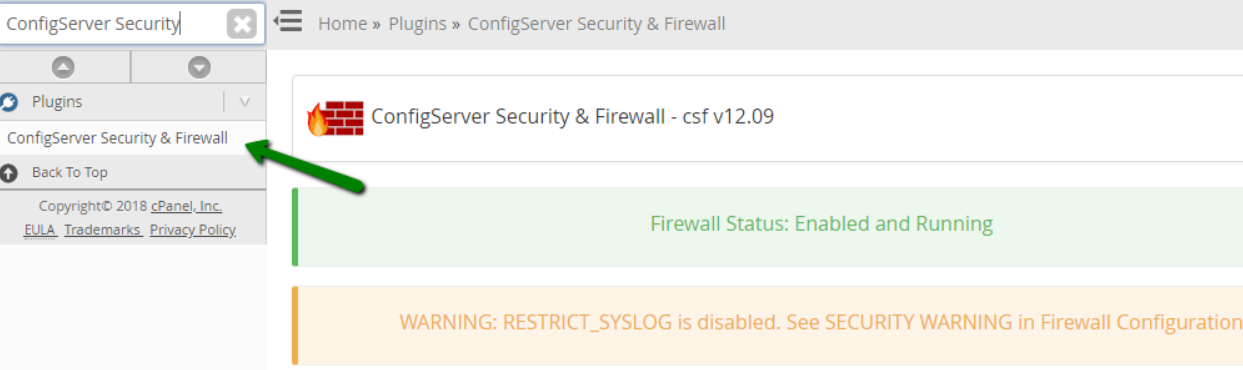
To disable such notifications, go to WHM >> Plugins section >> ConfigServer Security & Firewall.
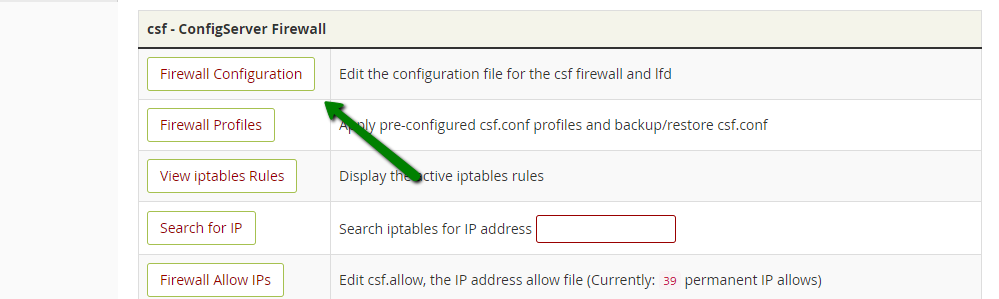
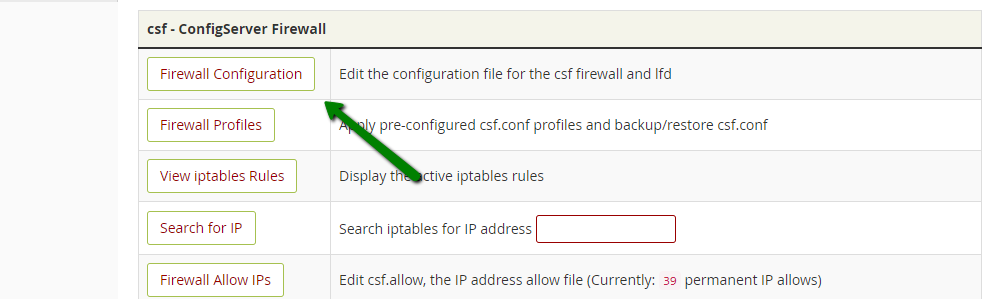
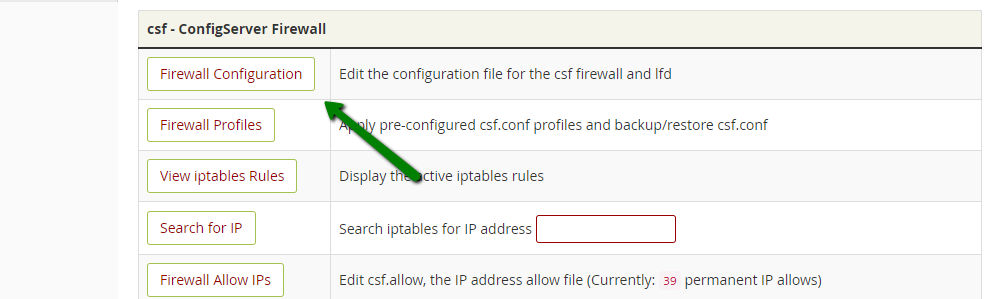
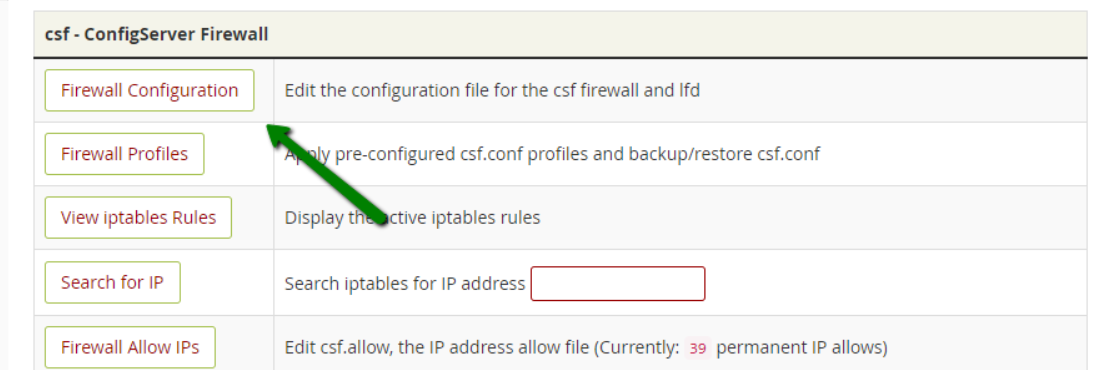
Now proceed to CSF >> Firewall Configuration.
There, find the PT_USERMEM and PT_USERTIME parameters and change their values to 0.
This will disable the notifications completely as these parameters define the threshold after which the notifications will be sent. However, we strongly recommended to keep them enabled so that you’re able to check whether that particular process is expected to use that much allotted resource.
You might feel that the default values are too low and you are getting flooded with notifications about valid processes, so you might want to change PT_USERMEM and PT_USERTIME to the values you feel will be the most appropriate.
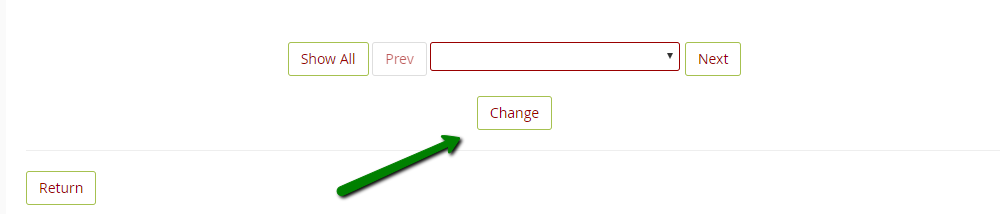
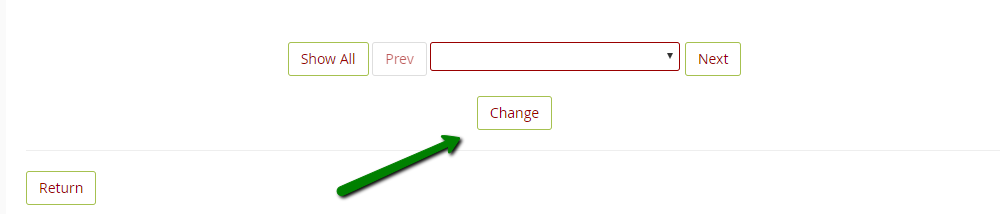
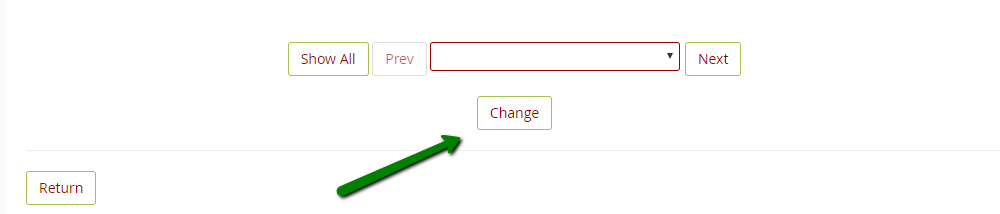
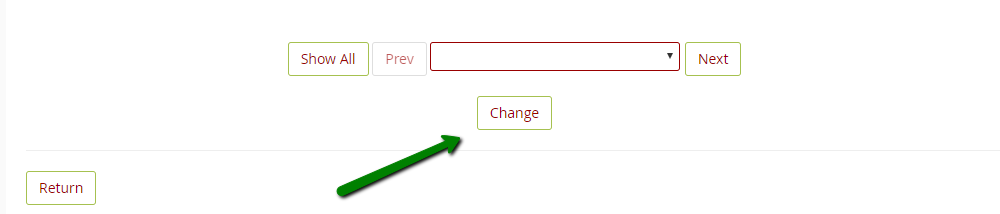
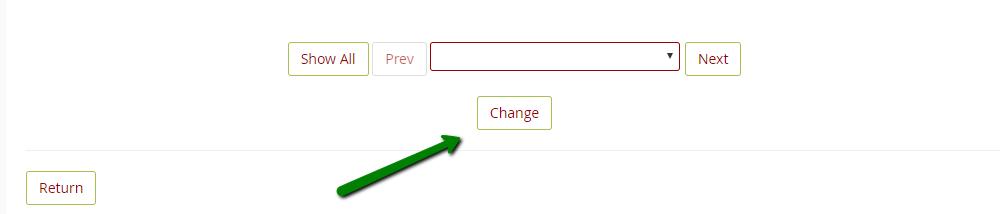
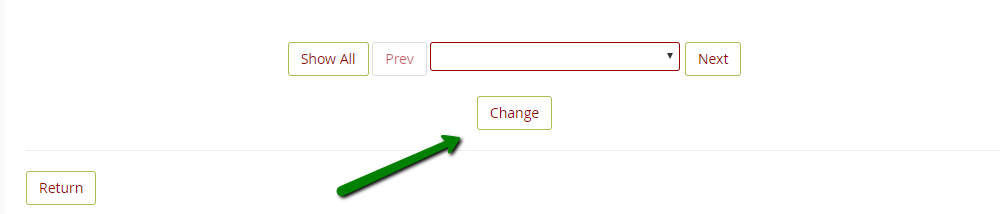
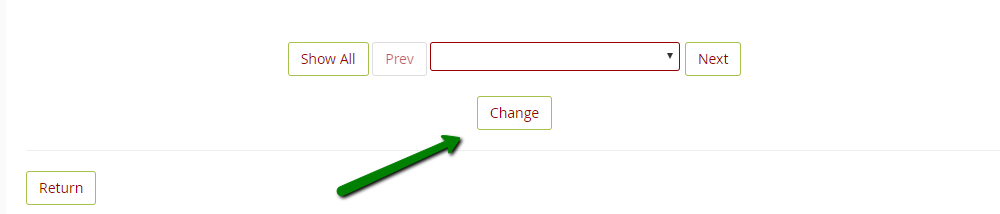
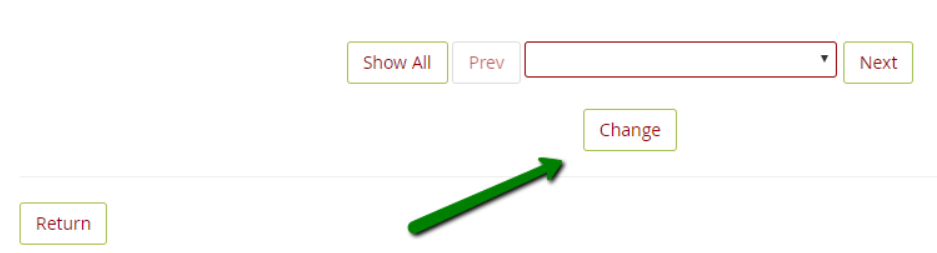
Once you have done this, scroll down and click on the Change button.
On the next page, you will see the Changes saved. You should restart both csf and lfd. message. Click Restart csf+lfd and the changes will be saved.
There is also an ignore list at /etc/csf/csf.pignore that can be used to either whitelist usernames or full paths to binaries. The following format should be used in the file:
exe:/full/path/to/file
user:username
cmd:command line
The file can be edited via SSH using your editor of choice.
After the changes are done, you need to reload CSF and restart LFD using the following SSH command:
csf -r or service lfd restart
2. System integrity alert
LFD has a feature in place to check for changes in certain system files. This helps to detect compromised files but also sends you an alert any time these files are changed by legitimate system updates. If you aren’t sure why these files are being changed, it’s important to check the server logs to determine whether the changes are the expected results of updates/other intentional changes or if there’s a compromised file that needs to be addressed.
These notifications are only sent once and, in most cases, are triggered by a system update. In this case, no further action from your side is needed.
By default, these notifications look like this:
From: root
To: root
Subject: lfd on [hostname]: System Integrity checking detected a modified system file
Time: [time]
The following list of files have FAILED the md5sum comparison test. This means that the file has been changed in some way. This could be a result of an OS update or application upgrade. If the change is unexpected it should be investigated.
[text]
- root in the From: and To: lines is usually replaced by root@
- [hostname] is replaced by the server's hostname
- [time] is replaced by the time at which the changes were detected
- [text] is replaced by some information concerning the detected changes
As for checking the server logs, you can check recent system updates for CentOS using this command:
yum history
For more detailed information about each update, you can use yum history info with the update ID (ID is to be found in the output of yum history).
The cPanel system update log files are stored in /var/cpanel/updatelogs.
We recommend to keep these types of notifications enabled so that you can investigate all unexpected changes as soon as possible. Still, if you wish to disable these notifications, you can do it in the following way:
Go to WHM >> Plugins >> ConfigServer Security & Firewall.
Then, proceed to CSF >> Firewall Configuration.
There, find the LF_INTEGRITY parameter and set its value to 0.
Once you have done this, scroll down and click the Change button.
On the next page, you will see the Changes saved. You should restart both csf and lfd. message. Click Restart csf+lfd and the changes will be saved.
3. Suspicious process alert
The Process Tracking option enables tracking of user’s and nobody’s processes and examines them for suspicious executable files or opened network ports (e.g., if it’s running from a deleted executable file or has network connections open). Its purpose is to identify potentially exploitative processes that are running on the server, even if they are obfuscated to appear as system services.
By default, these notifications look like this:
From: root
To: root
Subject: lfd on [hostname]: Suspicious process running under user [user]
Time: [time]
PID: [pid]
Account: [user]
Uptime: [uptime] seconds
Executable:
[exe]
Command Line (often faked in exploits):
[cmdline]
Network connections by the process (if any):
[sockets]
Files open by the process (if any):
[files]
Memory maps from the process (if any):
[maps]
- root in the From: and To: lines are usually replaced by root@
- [hostname] is replaced by the server's hostname
- [user] is replaced by the user the process is running under
- [time] is replaced by the time at which the process was detected as suspicious
- [pid] is replaced by the Process ID of the process
- [uptime] is replaced by the time the process has been running for
- [exe] is replaced by the executable file the process is running from
- [cmdline] is replaced by the command line command associated with the process
- [sockets] ID replaced by information about any network connections the process has open
- [files] ID replaced by a list of files the process has open
- [maps] ID replaced by a list of memory maps the process has open
We recommend that you keep these types of notifications enabled so that you can check whether or not the process is actually suspicious.
If you still wish to disable these notifications, you can do it in the following way:
Go to WHM >> Plugins section >> ConfigServer Security & Firewall.
Then, proceed to CSF >> Firewall Configuration.
There, you will find the PT_LIMIT parameter. Please set its value to 0.
Once you have done this, scroll down and click the Change button.
On the next page, you will see the Changes saved. You should restart both csf and lfd. message. Click Restart csf+lfd and the changes will be saved.
You can also add an executable file or command line path to /etc/csf/csf.pignore file.
The file can be edited via SSH using your editor of choice.
After the changes to the file are done, you need to reload CSF and restart LFD using the following command:
csf -r or service lfd restart
4. Alert about IP block
CSF/LFD automatically blocks IP addresses for certain configurable reasons. By default, any time the system blocks an IP address, it will send you an email to let you know which IP was blocked and why it was blocked.
Let’s look at how some of these notifications look, by default:
Login Failures:
From: root
To: root
Subject: lfd on [hostname]: blocked [ip]
Time: [time]
IP: [ip]
Failures: [ipcount]
Interval: [iptick] seconds
Blocked: [block]
Log entries:
[text]
- root in the From: and To: lines are usually replaced by root@
- [hostname] is replaced by the server's hostname
- [ip] is replaced by the blocked IP
The message itself includes the time the notification was sent, the IP address that was blocked, how many times that IP address failed the respective trigger rule, how long the IP address will be blocked for, and whether or not the IP address was temporarily or permanently blocked.
For example, if the IP address was permanently blocked, the following notification will be sent:
From: root
To: root
Subject: lfd on [hostname]: [ip] blocked permanently
Time: [time]
IP: [ip]
Temporary Blocks: [count]
Temporary blocks that triggered the permanent block:
[blocks]
- root in the From: and To: lines are usually replaced by root@
- [hostname] is replaced by the server's hostname
- [ip] is replaced by the blocked IP
The message also contains information about the time the permanent block was created and the amount of temporary blocks triggered.
We recommend that you first keep such notifications enabled to make sure that the firewall is configured correctly, blocking only the IP addresses you want blocked. Once you’ve confirmed that everything is OK, you might want to disable these types of notifications so that your mailbox doesn’t get flooded with too many emails or distract you from the more helpful ones.
To enable such notifications, please do the following:
Go to WHM >> Plugins section >> ConfigServer Security & Firewall.
Now proceed to CSF >> Firewall Configuration.
Here you will see the following parameters:
- LF_EMAIL_ALERT - sends an email alert if an IP address is blocked by one of the triggers.
- LF_PERMBLOCK_ALERT - sends an email alert if an IP address is permanently blocked. This happens if the IP address has been temporarily blocked more than a few times (to configure, use LF_PERMBLOCK_COUNT).
- LF_NETBLOCK_ALERT - sends an email alert if an IP network class was blocked (conditions of such blocks can be configured by editing the adjacent parameters).
- LF_DISTFTP_ALERT - sends an email alert if LF_DISTFTP is triggered. The LF_DISTFTP option will keep track of all successful FTP logins.
- It blocks all the IPs that are suspected in being involved into an FTP distributed attack. You can configure it by editing the parameters in the Distributed Attacks section.
- LF_DISTSMTP_ALERT - sends an email alert if LF_DISTSMTP is triggered. The same scenario applies as above, but for SMTP.
- LT_EMAIL_ALERT - sends an email alert if the account exceeds a certain number of hourly logins per IP address.
- CT_EMAIL_ALERT - sends an email alert if an IP address is blocked due to connectivity tracking.
If you do not want to be notified about certain IP address blocks, please set the corresponding parameter from the list above to OFF.
Once you have done this, scroll down and click the Change button.
On the next page, you will see the Changes saved. You should restart both csf and lfd. message. Click Restart csf+lfd and the changes will be saved.
5. Email queue size alert
LFD has a feature in place for watching the length of email queues. When many emails are sent from a server, the SMTP server automatically places them into an email queue where email messages await to be processed. The delivery starts from the first ones and then carries on with the others. If many messages accumulate in the email queue, this may lead to issues where emails are delivered with delays.
If you receive such a notification, it’s important to check what’s causing this situation. Many emails that get stuck in this email queue may indicate a security issue.
By default, these notifications look like this:
From: root
To: root
Subject: lfd on [hostname]: Email queue size alert
Time: [time]
[text]
- root in the From: and To: lines are usually replaced by root@
- [hostname] is replaced by the server's hostname
- [time] is replaced with the time when the long queue was first detected
We recommend that you leave these notifications enabled in order to immediately address any potential issues. If you wish to disable them, please follow these steps:
Go to WHM >> Plugins section >> ConfigServer Security & Firewall.
Now proceed to CSF >> Firewall Configuration.
There, locate the LF_QUEUE_ALERT parameter and set it to 0. Alternatively, you can set a threshold value from 0 to 5000 for these notifications to be sent.
Once you have done this, please scroll down and click the Change button.
On the next page, you will see the Changes saved. You should restart both csf and lfd. message. Click Restart csf+lfd and the changes will be saved.
6. Email script alert
Scripts usually involve the sendmail or exim binary. When this happens, certain lines will appear in the LFD mail log which detects and notifies you if it happens repeatedly.
By default, these notifications look like this:
From: root
To: root
Subject: lfd on [hostname]: Script Alert for [path]
Time: [time]
Path: [path]
Count: [count] emails sent
Sample of the first 10 emails:
[emails]
Possible Scripts:
[scripts]
- root in the From: and To: lines are usually replaced by root@
- [hostname] is replaced by the server's hostname
- [path] is replaced by the folder path found in the mail log
- [time] is replaced by the time the behavior was detected
- [count] is replaced by the number of emails detected
- [emails] is replaced by some relevant log lines
- [scripts] is replaced by LFD's estimate of which scripts might be involved. Unfortunately, such guesses are
- often inaccurate so it’s important to check which script is actually involved.
We recommend to keep these types of notifications enabled so that you can address any potential issues in a timely manner. You can also disable them following these steps:
Go to WHM >> Plugins section >> ConfigServer Security & Firewall.
Now proceed to CSF >> Firewall Configuration.
There, you will find the LF_SCRIPT_ALERT parameter. Set it to OFF.
Once you have done this, please scroll down and click the Change button.
On the next page, you will see the Changes saved. You should restart both csf and lfd. message. Click Restart csf+lfd and the changes will be saved.
7. Excessive processes alert
LFD also tracks the number of processes running under cPanel accounts, for example, PHP, CGI, SSH or cron jobs.
Each visitor who accesses a PHP page will generate an entry process, but these processes usually end quickly. It’s unlikely that 10 processes will be generated concurrently and at a single moment.
A large number of concurrent processes indicates high levels of traffic or an improperly-coded website that takes too long to finish one process. Additionally, this kind of situation happens when there are DDoS attacks on the website.
By default, these notifications look like this:
From: root
To: root
Subject: lfd on [hostname]: Excessive processes running under user [user]
Time: [time]
Account: [user]
Process Count: [number]
Process Information:
User: [user]
PID: [pid]
PPID: [ppid]
Run Time: [secs]
Memory: [kb]
RSS: [kb]
Executable [exe]
Command Line: [cmd]
If the traffic you have on the websites is legitimate, the notifications may be false-positive.
To modify the process limit or disable the notifications, go to WHM >> Plugins section >> ConfigServer Security & Firewall:
Now proceed to CSF >> Firewall Configuration.
There, you will find the PT_USERPROC parameter.
Set it to 0 if you want to stop receiving these notifications altogether. However, we recommend keeping them enabled in order to be notified if the process usage exceeds the allowed limit.
You might feel that the default value is too low and you are getting flooded with notifications about valid processes, so you might want to change PT_USERPROC to the value you feel will be the most appropriate.
Once you have done this, scroll down and click on the Change button.
On the next page, you will see the Changes saved. You should restart both csf and lfd. message. Click Restart csf+lfd and the changes will be saved.
That's it!
Categories
- cPanel Question 47
- cPanel Software Management 29
- cPanel Tutorials 13
- Development 29
- Domain 13
- General 19
- Linux Helpline (Easy Guide) 156
- Marketing 47
- MySQL Question 13
- News 2
- PHP Configuration 14
- SEO 4
- SEO 42
- Server Administration 84
- SSL Installation 54
- Tips and Tricks 24
- VPS 3
- Web Hosting 44
- Website Security 22
- WHM questions 13
- WordPress 148
Subscribe Now
10,000 successful online businessmen like to have our content directly delivered to their inbox. Subscribe to our newsletter!Archive Calendar
| Sat | Sun | Mon | Tue | Wed | Thu | Fri |
|---|---|---|---|---|---|---|
| 1 | 2 | 3 | ||||
| 4 | 5 | 6 | 7 | 8 | 9 | 10 |
| 11 | 12 | 13 | 14 | 15 | 16 | 17 |
| 18 | 19 | 20 | 21 | 22 | 23 | 24 |
| 25 | 26 | 27 | 28 | 29 | 30 | |
Recent Articles
-

Posted on : Sep 17
-

Posted on : Sep 10
-

Posted on : Aug 04
-

Posted on : Apr 01
Tags
- ts
- myisam
- vpn
- sql
- process
- kill
- tweak
- server load
- attack
- ddos mitigation
- Knowledge
- layer 7
- ddos
- webmail
- DMARC
- Development
- nginx
- seo vpn
- Hosting Security
- wireguard
- innodb
- exim
- smtp relay
- smtp
- VPS Hosting
- cpulimit
- Plesk
- Comparison
- cpu
- encryption
- WHM
- xampp
- sysstat
- optimize
- cheap vpn
- php-fpm
- mariadb
- apache
- Small Business
- Error
- Networking
- VPS
- SSD Hosting
- Link Building
- centos
- DNS
- optimization
- ubuntu